The Samsung Galaxy Note series is almost a decade old. Within that time-frame the stylus-donning handset has brought forth plenty of new technologies – such as curved screen and edge control – which have, perhaps unsurprisingly, become the relative norm in smartphone land. As a result …
Earlier this year, Microsoft’s Surface head Panos Panay started leading the new Windows + Devices group at Microsoft. This allows Panos Panay to oversee the work on Microsoft’s Surface and Windows 10, and other Windows product like Windows 10X. While Windows 10 is more popular than …
Last June, Arcade1Up announced it would release Ms. Pac-Man and X-men vs. Street Fighter 3/4th scale cabinets. Now the company is ready to take pre-orders, but it has two surprises as well. Arcade1Up is also taking pre-orders on a Marvel vs. Capcom machine, and both fighting …
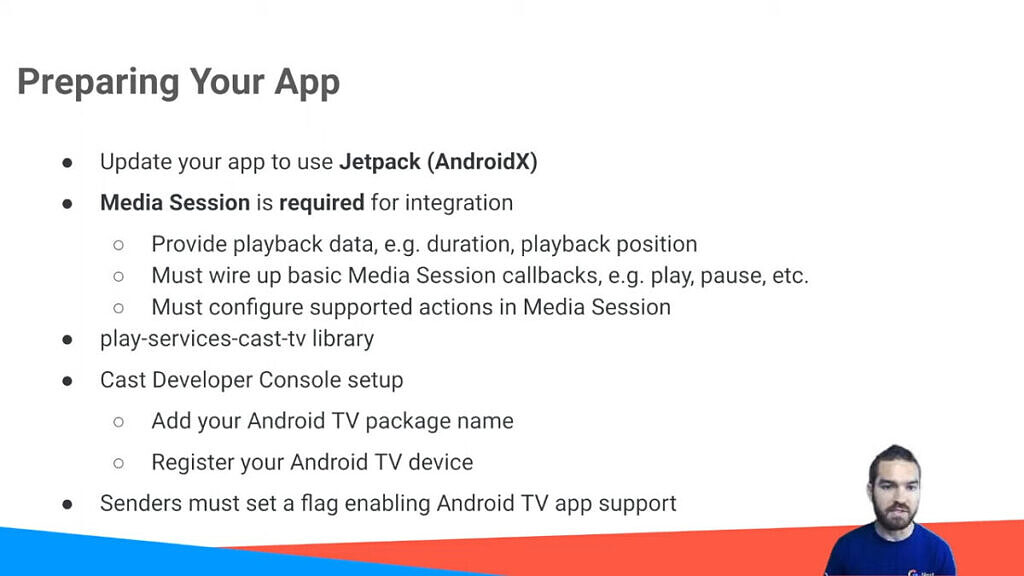
Casting video content to your Android TV device will hopefully feel more native in the near future thanks to the introduction of Cast Connect. As pointed out by Twitter user Android TV Guide, this new feature will have the benefit of making it possible to use …
Huawei’s second flagship smartphone series is expected before the year is out in the Mate 40 and Mate 40 Pro and whilst leaks have been few and far between, some renders have now appeared online giving us an indication of what they might look like. The …
Jetbrains announced the release of its Python IDE, PyCharm 2017.3.2, a day ago. Here’s how you can install it in Ubuntu 16.04 and higher. Changes in PyCharm 2017.3.2 include: Type annotation ahead of time. You can’t put an inline type annotation when defining a variable in …
Nowadays people don’t want to remain content with a single smartphone for long. They not only change their handsets, but also change the ecosystem. As long as you are changing the handsets, there is not much hazard to deal with. But if you are moving …
Credential Guard is a feature that uses virtualization-based security to separate certain secrets so as to make them accessible to only privileged system software. The secrets are always suceptible to cyber threats owing to the increasing degree of hacking. Hence unauthorized access is deleterious to …
DVD Ripping is a common task that all computer users are aware of. Now that almost all of us have smartphones in our possession, it’s very obvious that we would want to have the movies from our old DVD collections to our smartphones. That’s when …
These days we have passwords and patterns to protect all of our devices. Most of them come with specifications of their own because of which we often have to remember a whole host of passwords, pins, etc, to access all our different devices and accounts. …